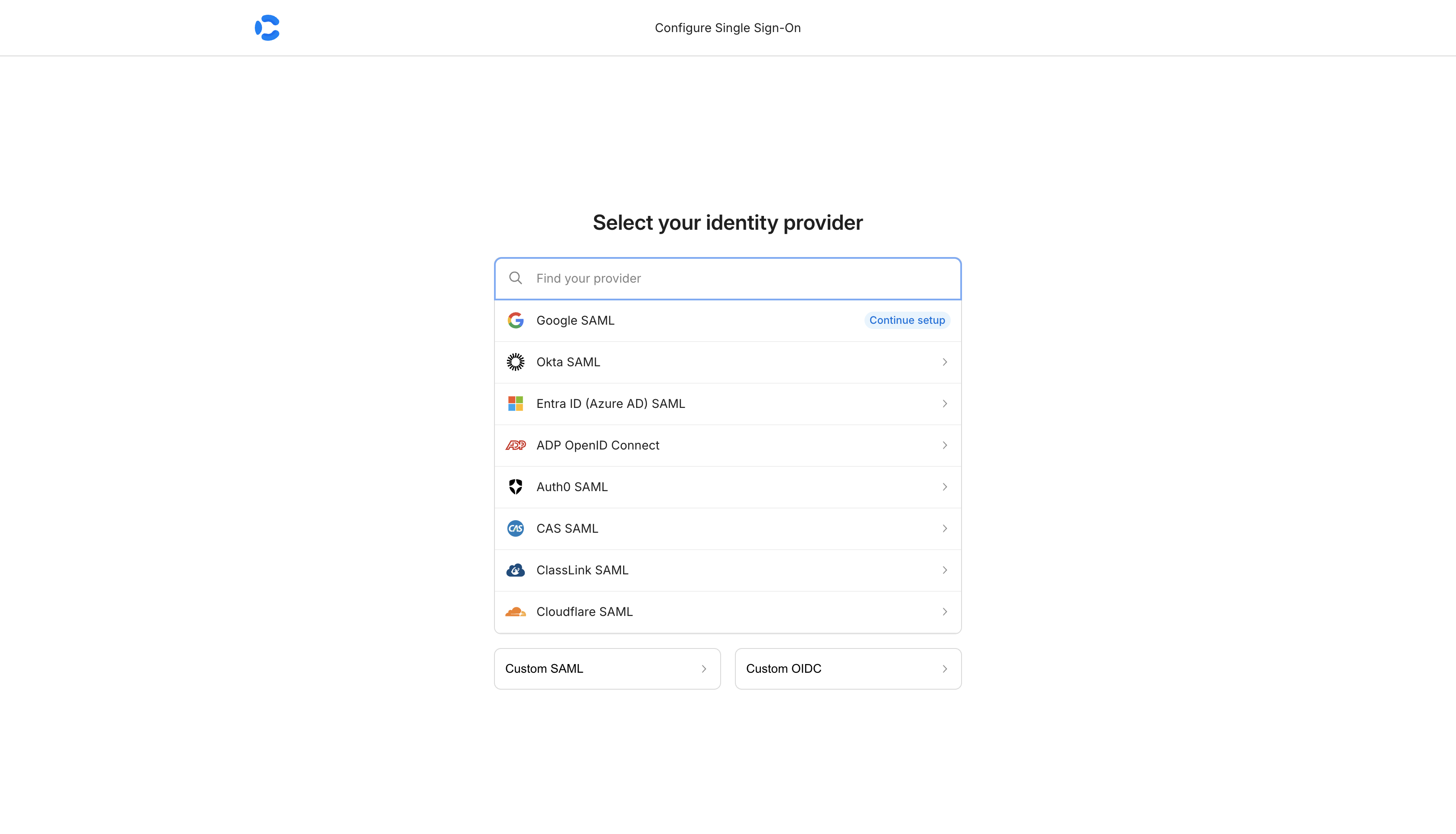
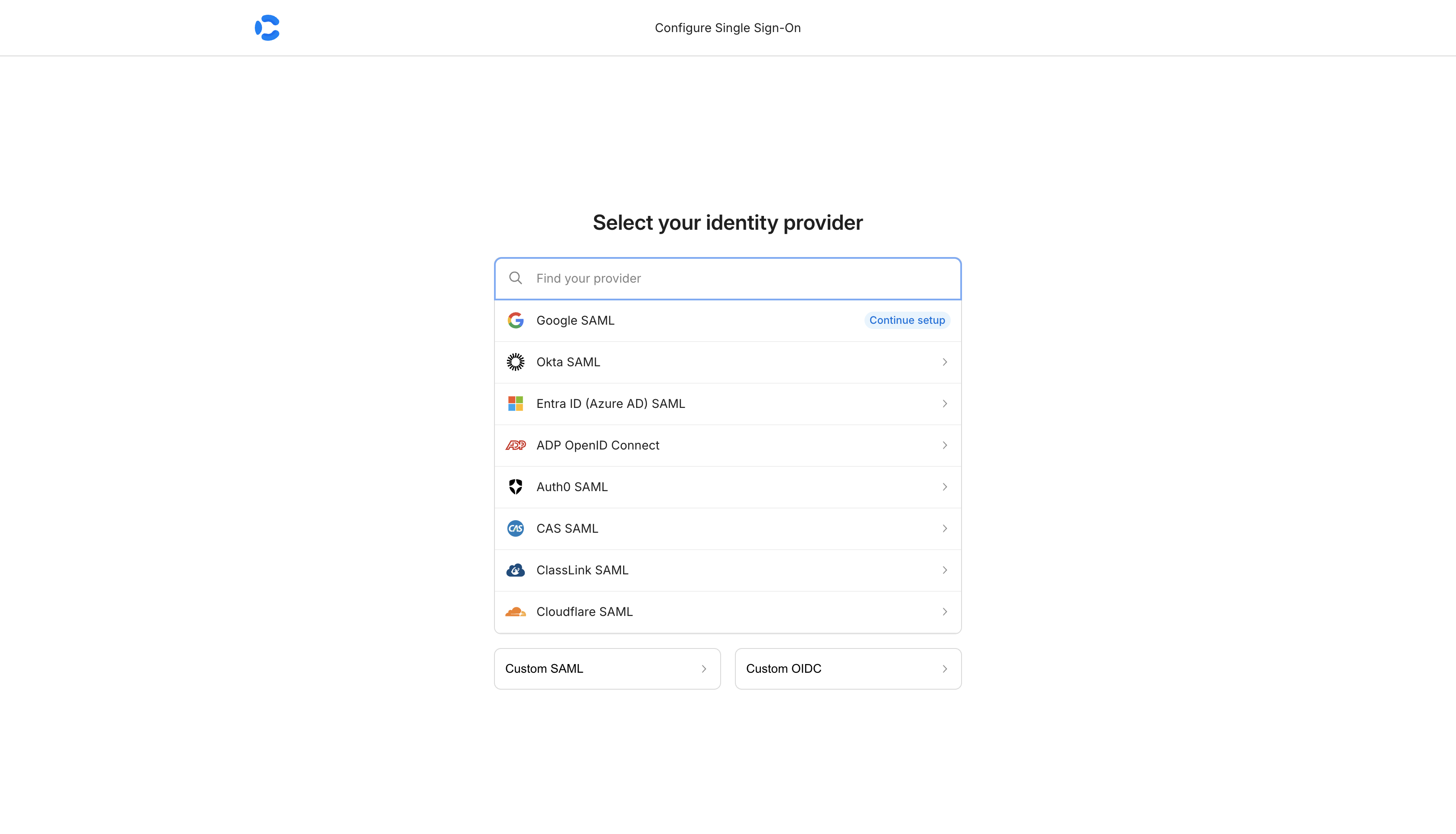
SAML SSO lets your team sign in to Convoy using your organisation’s identity provider (IdP). Supported providers include Google, Okta, Entra ID (Azure AD), Auth0, ADP, CAS, ClassLink, Cloudflare, and any custom SAML 2.0 or OIDC-compatible provider.Documentation Index
Fetch the complete documentation index at: https://getconvoy.io/docs/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
- A Premium license with the SSO feature.
- A SAML 2.0-compatible identity provider.
Setup
Enable SSO in your config
Add your license key and enable SSO in Alternatively, use environment variables:
convoy.json:convoy.json
Configure your SAML connection
In the Convoy dashboard, go to Organisation Settings and click Configure SSO.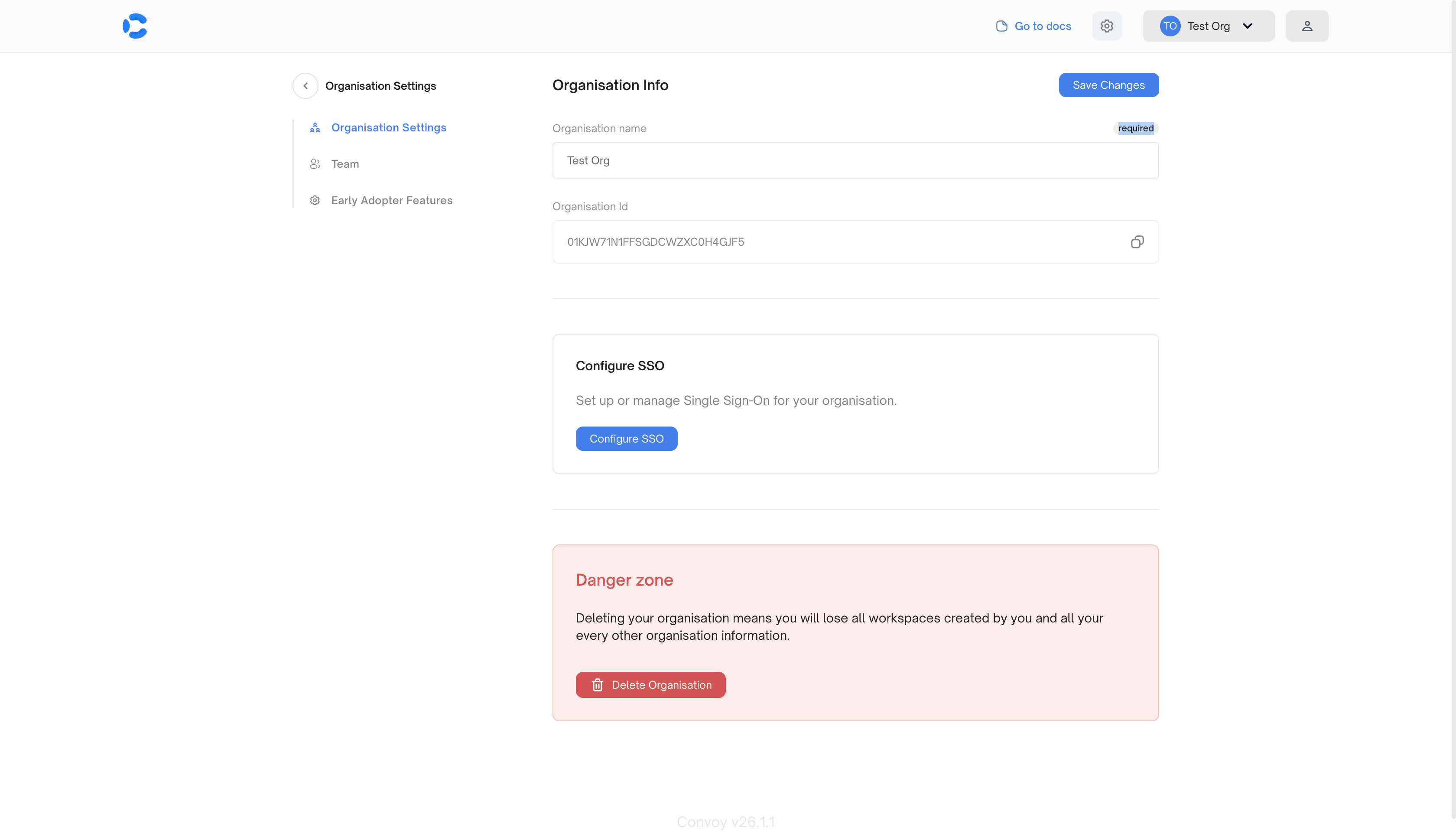
If you need multiple SAML connections, reach out to us at [email protected].
How It Works
- You click Login with SSO on the login page.
- Convoy redirects you to your IdP for authentication.
- You authenticate with your IdP.
- The IdP sends a SAML assertion back to Convoy.
- Convoy validates the assertion and issues a short-lived token.
- Your browser lands on Convoy’s
/samlcallback with this token. - Convoy exchanges the token for a session and logs you in.
Troubleshooting
”auth.sso.redirect_url is required for SSO login”
Convoy couldn’t determine where to redirect after authentication. Set thehost field in your config to your Convoy instance’s public URL:
auth.sso.redirect_url explicitly.
Use the UI callback path (/saml) rather than API-prefixed paths (/ui/...). If you deploy with a root_path, include it (for example, https://convoy.yourcompany.com/convoy/saml).
SSO button doesn’t appear on the login page
- Check that your license includes the SSO feature.
- Verify
auth.sso.enabledistrue. - Restart Convoy after config changes.
”Authentication failed” after IdP redirect
- Check that the SAML connection in the SSO portal is configured correctly.
- Ensure the ACS URL and SP Entity ID in your IdP match the values shown in the SSO portal.
Blank page or errors after callback
- Make sure you’re running the latest version of Convoy.
- Clear your browser cache and try again.
Related
- Licensing — Get and configure a Premium license
- Google SSO — Sign in with Google OAuth
- RBAC — Manage permissions after sign-in